SOC Audits
Securing Trust in a Digital Age
Navigating the complexities of compliance and security can be challenging in today’s digital age. Without proper controls and oversight, you risk operational inefficiencies, financial discrepancies, and potential regulatory penalties. Most importantly, ignoring these issues can lead to reputational damage and loss of stakeholder trust, which are critical to your business’s success.
As cyber threats become more sophisticated, ensuring robust cybersecurity measures is essential. Outdated or inadequate security practices can leave your organization vulnerable to breaches, compromising sensitive data and disrupting business operations. This not only affects your bottom line but also erodes stakeholder confidence.
SOC Audits, including SOC 1, SOC 2, SOC 3, and SOC for Cybersecurity, provide the critical insights and assurance needed to mitigate these risks. Whether it’s a Type 1 or Type 2 engagement, these audits help identify and address vulnerabilities, ensuring your organization meets industry standards and secures its operations effectively. Integrating these audits into your security strategy and internal controls fortifies your defenses, providing a solid foundation for trust and success.
Provide stakeholders unwavering confidence in the strength of your controls.
SOC Support for Internationally Based Companies Operating in the United States
At McKonly & Asbury, we understand the unique challenges and responsibilities facing internationally owned companies operating within the United States. Our SOC audit services—ranging from SOC 1 and SOC 2 to SOC 3 and SOC for Cybersecurity—are tailored to support the needs of these businesses, providing scalable, efficient, and actionable solutions that help you stay secure, compliant, and trusted in today’s complex digital environment.
SOC Solutions
SOC 1 audits focus on the internal controls over financial reporting. These audits are essential for organizations that provide services impacting their clients’ financial statements. By evaluating and ensuring the effectiveness of these controls, the SOC 1 audit helps build trust with clients and stakeholders, demonstrating a commitment to financial accuracy and integrity.
SOC 2 audits address the controls relevant to security, availability, processing integrity, confidentiality, and privacy. These audits are crucial for organizations that handle sensitive data and need to demonstrate their commitment to protecting this information. SOC 2 audits provide assurance that the organization’s systems are secure, reliable, and operate with integrity.
SOC 3 audits are the public part of a SOC 2 audit, intended for a general audience. These audits provide a high-level overview of the organization’s controls in a way that is easily understood by clients and the public. These reports are often used for marketing purposes to demonstrate security and trustworthiness to clients and stakeholders.
SOC for Cybersecurity audits provide a framework for evaluating an organization’s cybersecurity risk management program. These audits help identify and address potential vulnerabilities, ensuring robust cybersecurity measures are in place. By undergoing a SOC for Cybersecurity audit, organizations can demonstrate their commitment to protecting sensitive data and maintaining strong security postures against evolving cyber threats.
SOC 2 Reporting & Other Services
How Can We Help?
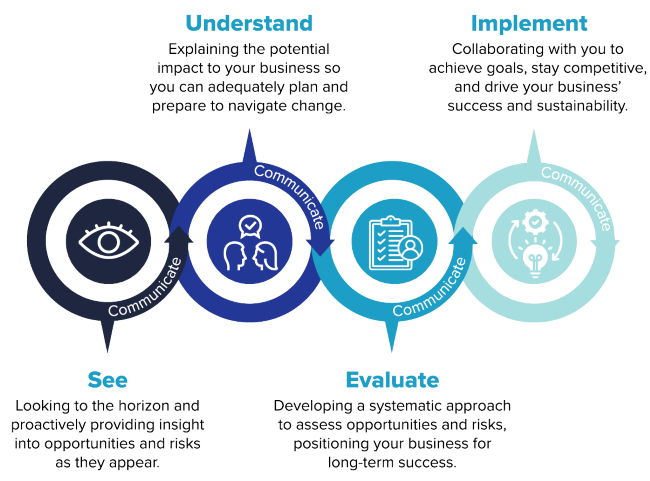
By leveraging our SOC audits and reports and technology solutions, you can expect a proactive approach that protects your organization and positions you for growth and success. From detailed risk assessments to tailored solutions and continuous support, these solutions ensure your IT systems and processes are effective and up to date: